RISC-V 솔루션 채택 전에 파악해야 하는 보안 이슈들
기사입력 2020.02.04 16:35
개방형 ISA인 RISC-V 프로세서 늘어나
IoT 보안 위협, 기존 애플리케이션보다 치명적
멀티존 시큐리티, RISC-V 내장 보안 솔루션
RISC-V는 축소 명령어 집합 컴퓨터(RISC) 기반 개방형 명령어 집합(ISA)이다.
대부분의 ISA와 달리 어떠한 목적으로든 자유롭게 사용할 수 있으며, 누구든지 RISC-V 칩과 소프트웨어를 설계, 제조, 판매할 수 있도록 허가되어 있다. 무료면서 개발자가 원하는 설계 방향대로 성능에 맞게 기능을 구현할 수 있어 크게 주목받고 있다.
가령 마이크로칩은 지난 12월, RISC-V 기반 ‘폴라파이어(PolarFire) SoC FPGA’를 발표했다. 이 제품은 RISC-V 기반 CPU 클러스터와 함께 리눅스 및 실시간 애플리케이션을 지원하는 결정론적 L2 메모리 서브 시스템을 갖췄다.

Arm 및 x86 아키텍처 기반이 아닌 RISC-V 기반 칩셋 및 솔루션의 활용도가 높아지면서 보안에 관한 관심도 커지고 있다.
특히 IoT 기기와 시스템에 대한 보안 위협은 기존 보안 위협보다 치명적이다. 가전, 차량, 로봇, 설비 등의 오작동은 인명피해를 초래할 수 있다. IoT 기기와 시스템은 서로 네트워크로 연결되기 때문에 다른 기기와 시스템에도 영향을 미치거나 예상하지 못한 문제를 일으킬 수 있다.
마이크로칩의 시니어 임베디드 솔루션 엔지니어인 김지훈 과장은 4일, ‘RISC-V 애플리케이션에서의 MultiZone 보안 구현’이란 제목의 웨비나에서 RICS-V를 가장 안전한 플랫폼으로 만드려는 멀티존(MultiZone) 시큐리티를 소개했다.
헥스파이브(HEX-Five) 시큐리티가 개발하는 멀티존(MultiZone) 시큐리티는 RISC-V 기반 칩셋에 적용할 수 있는 내장 보안 솔루션이다. 데이터, 코드 및 주변 장치를 완벽하게 제어할 수 있는 무제한 보안 도메인에 대해 정책 기반의 하드웨어 적용 분리를 제공한다.
기존 솔루션과 달리 추가 하드웨어, 전용 코어 또는 복잡한 프로그래밍 모델이 필요하지 않다. 안전 및 보안을 달성하기 위해 오픈소스 라이브러리, 타사 바이너리 및 레거시 코드를 몇 분 안에 구성할 수 있다.
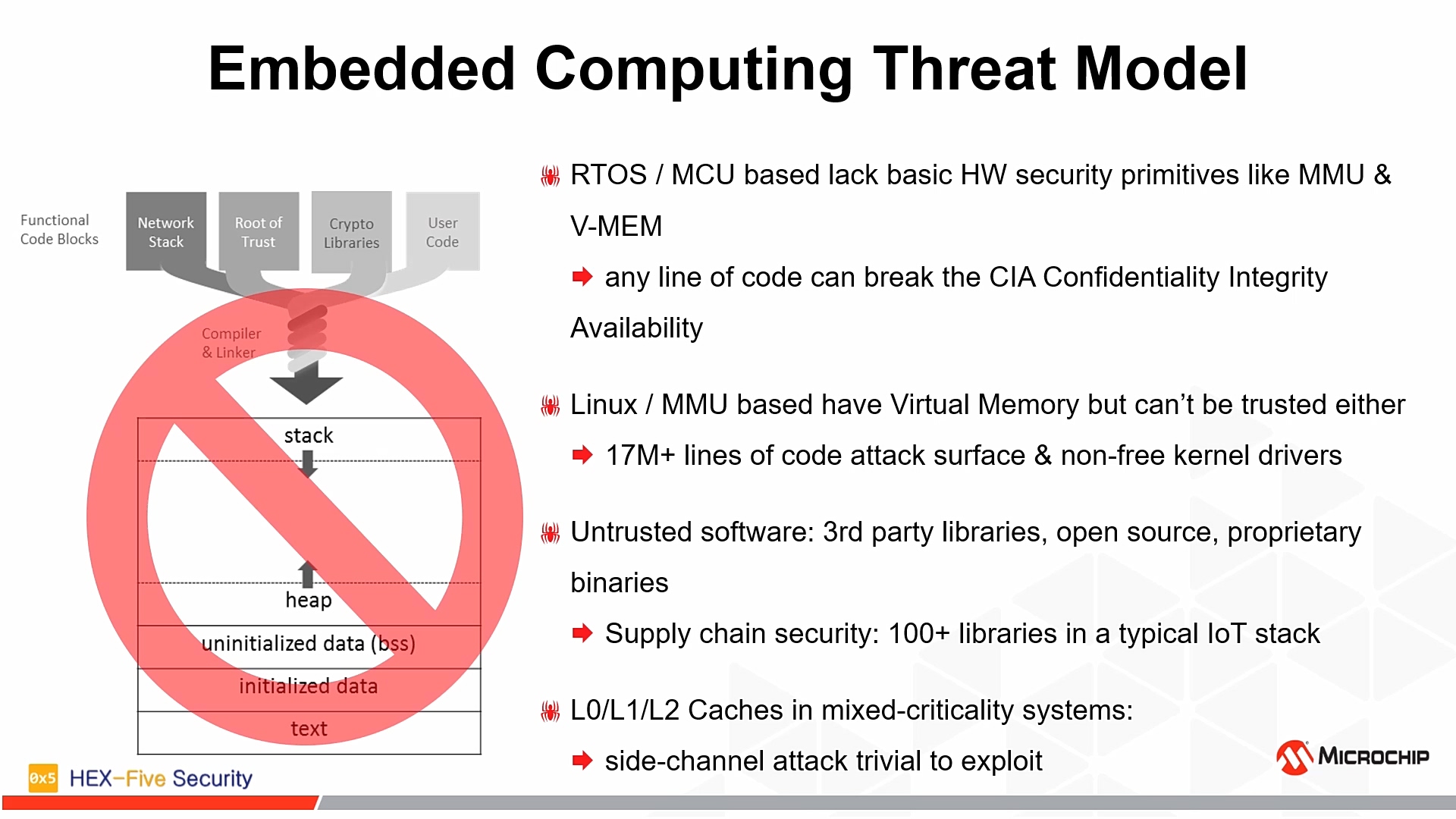
▲임베디드 컴퓨팅 위협 모델 (자료=마이크로칩)
김 과장은 임베디드 컴퓨팅 위협 모델을 비롯하여 RICS-V 하드웨어 시큐리티 프리미티브, 멀티존 트러스트 실행환경, 마이크로칩 폴라파이어 SoC FPGA를 예제로 한 보안 IoT 스택 설명, 멀티존 시큐리티가 실제로 프로세서 내부에서 하는 보안 역할 등을 설명했다.
현재 멀티존은 오픈소스 API로 제공된다. 자유롭고 개방된 표준이다. 멀티존이 제공하고 있는 상업적 구현은 현재 시장에서 사용할 수 있는 유일한 것으로, 혼합된 중요도 및 목적에 맞게 설계된 보안 시스템을 위해 설계되었다.
5G, AI 등의 활성화로 IoT 서비스의 본격적인 범람이 점쳐지는 가운데, 자사 애플리케이션에 최적화된 저전력 IoT 프로세서를 저렴한 가격으로 제작하려는 움직임이 일고 있다. 이로 인해 RICS-V 프로세서에 관한 관심이 늘고 있으며, IoT의 기본적인 특성인 연결성으로 인한 보안 이슈 역시 함께 늘어나고 있다.
개발자는 향후 개발할 IoT 애플리케이션의 원활한 동작을 위해 RICS-V 기반 프로세서와 이와 관련한 보안 솔루션에 대한 지식을 꾸준히 습득하여야 할 것이다.
한편, 마이크로칩은 ‘마이크로칩 시큐리티 웨비나 시리즈’ 중 첫 번째 편이었던 이번 웨비나에 이어 3월 3일, ‘클라우드 세계에서의 지적재산권(IP) 보호’에 대해 다룰 예정이다.
이수민 기자
클라우드 세계에서의 지적재산권(IP) 보호
2020-03-03 10:30~12:00
Microchip Technology Inc. / 엄명흠 차장
많이 본 뉴스
[열린보도원칙] 당 매체는 독자와 취재원 등 뉴스이용자의 권리 보장을 위해 반론이나 정정보도, 추후보도를 요청할 수 있는 창구를 열어두고 있음을 알려드립니다.
고충처리인 장은성 070-4699-5321 , news@e4ds.com

.png)



.jpg)