테슬라 BLE 잠금 장치, 해킹 취약점 드러나
기사입력 2022.05.19 16:25
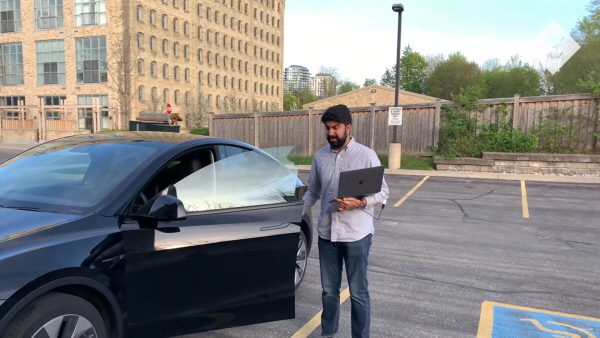
▲NCC 그룹 연구원이 노트북과 연결된 장치로 테슬라 잠금을 해제했다. (사진: The telegraph 유튜브 영상 캡처)
노트북 연결 소형 장치로 잠금 해제 후 주행까지
지난해 사이버 보안 공격, 자동차 관련 28%
테슬라 자동차를 포함한 BLE(Bluetooth Low Energy)를 이용하는 전 세계 수백만 개의 디지털 잠금장치가 해킹 취약점을 가지고 있다는 사실이 밝혀졌다.
로이터 통신은 사이버 보안 관련 회사인 NCC 그룹 연구원이 노트북에 부착된 작은 장치로 2021년식 테슬라 모델Y 차량의 잠금을 해제하고 운전을 하는 영상을 17일 공유했다.
NCC 그룹은 자동차뿐만 아니라 스마트홈 잠금장치도 같은 방식으로 해킹할 수 있다며 BLE 프로토콜의 취약점을 증명했다고 전했다.
이어 이번에 밝혀진 취약점이 소프트웨어 패치로 수정될 수 있는 버그가 아니라며 BLE 블루투스는 본래 잠금 장치 목적에 사용하도록 설계된 것도 아니라고 강조했다.
이 해킹 기법이 좋지 않은 목적으로 사용됐을 경우 어떤 일이 발생할지 감히 상상도 할 수 없다.
영상에서는 단순히 자동차 잠금을 해제하는 데서 그쳤지만 커넥티드 카가 대세가 될 미래에서 해킹의 위험성은 매우 크다.
커넥티드 카는 해커의 공격으로 △악성 소프트웨어 △데이터 조작 △하드웨어 수준의 물리적 공격과 같은 위협에 노출될 수 있으며, △차량 운전자의 안전을 위협하고 △개인적인 데이터 손실이 일어날 수 있으며 △제조사 비즈니스에도 영향을 미칠 수 있다.
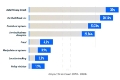
특히 2021년에 일어난 사이버 보안 공격 현상 중 차량 도난과 내부 제어 시스템을 탈취하는 공격이 28.4%로 데이터 유출(30%) 다음으로 많이 발생했다.
이경수 인피니언 과장은 e4ds 웨비나에서 ‘자동차 사이버 보안의 현재와 미래 및 인피니언의 대응 방안’에 대해 발표하며 “많은 표준 기관과 자동차·반도체 제조사들이 협력해서 오토모티브 사이버 시큐리티에 대한 가이드라인, 스탠다드, 레귤레이션(Regulation) 등의 활동을 하고 있다”고 전했다.
이어 “보안에 완벽이란 없다. 계속적으로 새로운 위협이 발생하기 때문에 이를 분석하여 보완하고 유지하고 관리하는 것이 중요한 부분”이라고 전했다.
로이터 통신은 사이버 보안 관련 회사인 NCC 그룹 연구원이 노트북에 부착된 작은 장치로 2021년식 테슬라 모델Y 차량의 잠금을 해제하고 운전을 하는 영상을 17일 공유했다.
NCC 그룹은 자동차뿐만 아니라 스마트홈 잠금장치도 같은 방식으로 해킹할 수 있다며 BLE 프로토콜의 취약점을 증명했다고 전했다.
이어 이번에 밝혀진 취약점이 소프트웨어 패치로 수정될 수 있는 버그가 아니라며 BLE 블루투스는 본래 잠금 장치 목적에 사용하도록 설계된 것도 아니라고 강조했다.
이 해킹 기법이 좋지 않은 목적으로 사용됐을 경우 어떤 일이 발생할지 감히 상상도 할 수 없다.
영상에서는 단순히 자동차 잠금을 해제하는 데서 그쳤지만 커넥티드 카가 대세가 될 미래에서 해킹의 위험성은 매우 크다.
커넥티드 카는 해커의 공격으로 △악성 소프트웨어 △데이터 조작 △하드웨어 수준의 물리적 공격과 같은 위협에 노출될 수 있으며, △차량 운전자의 안전을 위협하고 △개인적인 데이터 손실이 일어날 수 있으며 △제조사 비즈니스에도 영향을 미칠 수 있다.
특히 2021년에 일어난 사이버 보안 공격 현상 중 차량 도난과 내부 제어 시스템을 탈취하는 공격이 28.4%로 데이터 유출(30%) 다음으로 많이 발생했다.
이경수 인피니언 과장은 e4ds 웨비나에서 ‘자동차 사이버 보안의 현재와 미래 및 인피니언의 대응 방안’에 대해 발표하며 “많은 표준 기관과 자동차·반도체 제조사들이 협력해서 오토모티브 사이버 시큐리티에 대한 가이드라인, 스탠다드, 레귤레이션(Regulation) 등의 활동을 하고 있다”고 전했다.
이어 “보안에 완벽이란 없다. 계속적으로 새로운 위협이 발생하기 때문에 이를 분석하여 보완하고 유지하고 관리하는 것이 중요한 부분”이라고 전했다.
많이 본 뉴스
[열린보도원칙] 당 매체는 독자와 취재원 등 뉴스이용자의 권리 보장을 위해 반론이나 정정보도, 추후보도를 요청할 수 있는 창구를 열어두고 있음을 알려드립니다.
고충처리인 장은성 070-4699-5321 , news@e4ds.com