PKI 채택이 늘면서 데이터 보호를 위한 기업의 인프라 규모와 범위도 커진 것으로 드러났다. 엔트러스트가 발표한 '2020 글로벌 PKI 및 IoT 동향 보고서'에 따르면, PKI는 클라우드, 모바일 기기, 본인 인증, IoT 등 주요 디지털 이니셔티브에 강력한 보안을 제공하며 IT 인프라의 핵심으로 자리잡았다.
데이터 보호 위한 기업 인프라 규모 날로 커져
기업 관리할 인증서 숫자, '19년 대비 43% 증가
IoT 단말, 플랫폼, 스토리지 암호화 33%에 그쳐
공개 키 기반 구조(Public key Infrastructure; PKI) 채택이 늘면서 데이터 보호를 위한 기업의 인프라 규모와 범위도 커진 것으로 드러났다.
엔트러스트는 9일, '
2020 글로벌 PKI 및 IoT 동향 보고서'를 발표하며 이같이 밝혔다. 보고서는 한국을 포함 전 세계 17개 국가, 1,900여 명의 IT 보안 전문가 대상 설문 결과를 바탕으로 발간됐다.
보고서에 따르면, PKI는 클라우드, 모바일 기기, 본인 인증, IoT 등 주요 디지털 이니셔티브에 강력한 보안을 제공하며 IT 인프라의 핵심으로 자리잡은 것으로 나타났다. 디지털 의존도가 높아지고 사이버 공격이 정교해지며 기업이 데이터에 대한 접근 권한 설정, 사용자 시스템 기기 인증에 PKI 기술을 활용하고 있는 것이다.
올해 PKI 기술 채택의 주요 동인으론 응답자의 47%가 IoT를 꼽았다. 지난 5년간 IoT 보안을 위해 PKI 기술을 도입한 사례는 26% 증가했다. 클라우드 기반 서비스가 PKI 도입을 이끌었다는 응답자는 44%로 나타났다.
◇ 클라우드 및 인증 분야에서 PKI 이용 급증
조사에 의하면, 응답자의 84%가 PKI를 일반 사용자용 웹사이트 및 서비스의 TLS/SSL 인증에 사용했다고 밝혔다. 이는 가장 많은 수치다.
퍼블릭 클라우드 기반 애플리케이션은 82%로 전년 대비 27% 증가하며 가장 높은 연간 성장률을 보였다. 한국은 특히 퍼블릭 클라우드 기반 애플리케이션에 PKI를 사용한 비율이 96%로 매우 높았다. 기업 사용자 인증은 70%로 전년 대비 19% 늘었다.
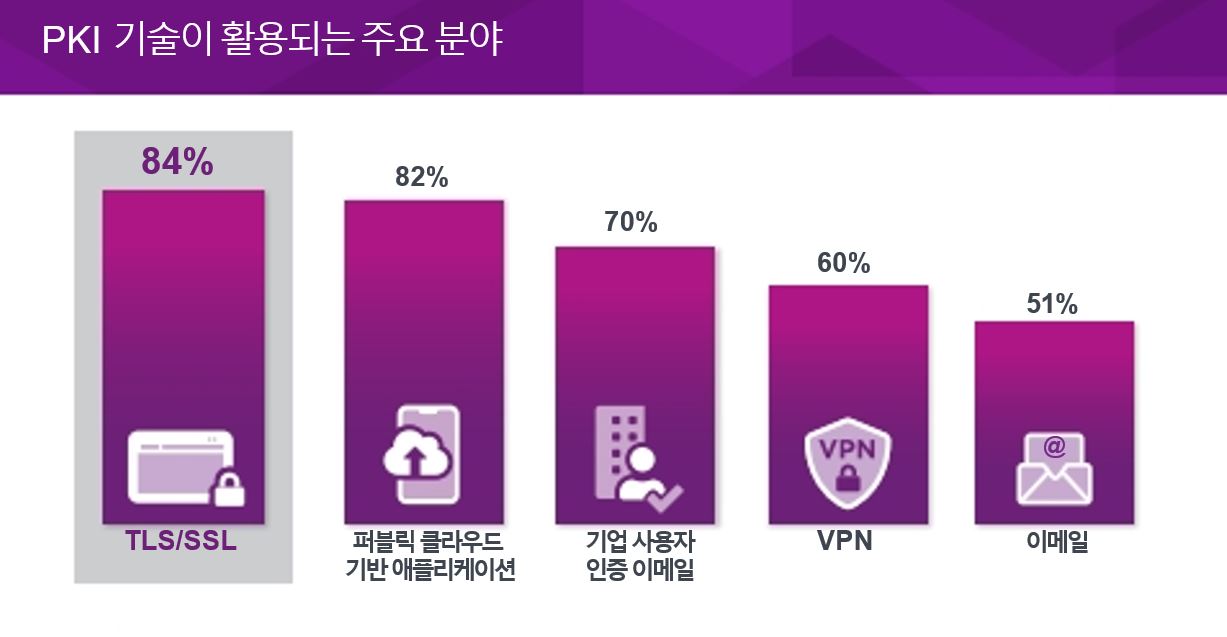
▲ PKI 기술이 활용되는 주요 분야 [그래프=엔트러스트]
기업이 관리해야 하는 인증서 평균 개수는 5만6,192개로 전년 3만9,197개 대비 43% 늘었다. 이는 인증서 유효기간을 줄이는 추세와 클라우드 및 기업 사용자 인증 용도가 급격히 증가한 데 따른 것으로 분석된다.
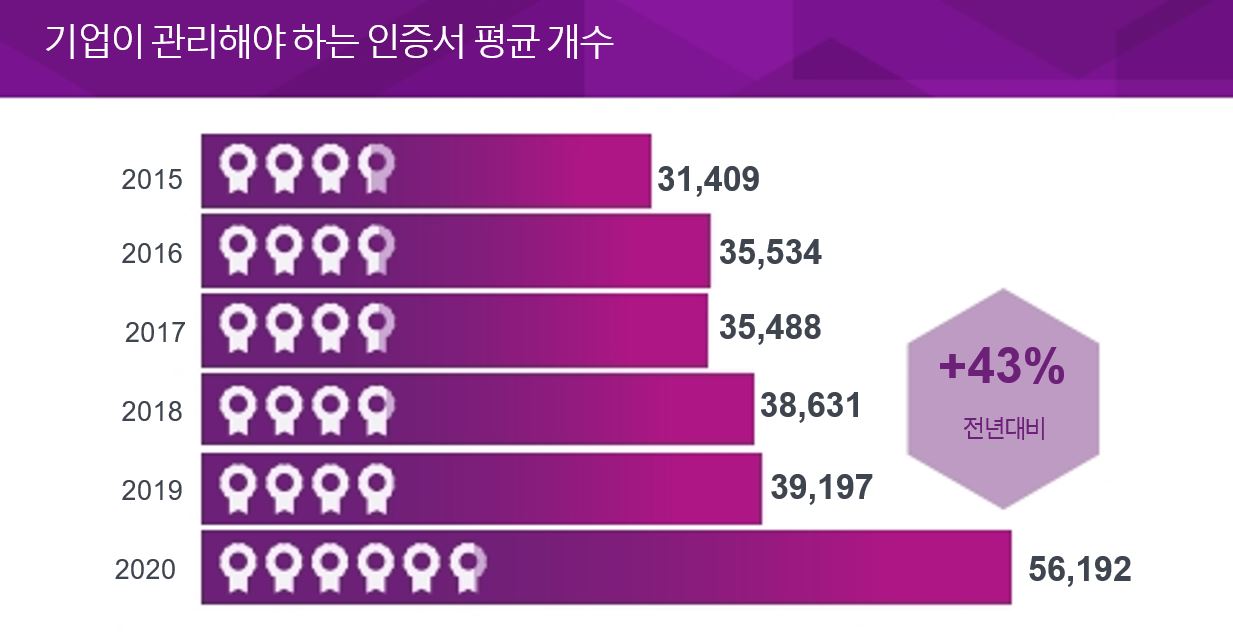
▲ 기업이 관리해야 하는 인증서 평균 개수 [그래프=엔트러스트]
PKI 기술의 당면 과제로 응답자 52%가 PKI 보안 역량 결여를 들었으며(전년 대비 16% 증가) 사이버 보안에 대한 전문 지식, 보안 및 운영 모범사례를 기반으로 기업 맞춤형 로드맵을 만들 PKI 전문 인력의 필요성이 제기됐다. 기존 애플리케이션을 변경할 수 있는 역량 부족(51%), 기존 PKI로 신규 애플리케이션을 지원할 수 없다는 점(51%)도 꼽혔다.
PKI 도입∙관리에 대해 응답자는 명확한 업무 권한이 없고, 역량 및 자원 부족 같은 조직적 문제로 어려움을 겪고 있다고 답했다. PKI 도입은 일부 국가에서 온프레미스(on-premise)보다 서비스 형태가 선호되며 다각화된 것으로 나타났다.
응답자는 PKI의 변화와 불확실성을 가져오는 주요 요인으로 IoT(52%), 외부 규정 및 표준(49%)을 들었다. 응답자의 24%는 규제 환경이 PKI 기술을 적용한 애플리케이션 도입을 더욱 필요로 한다고 답했다.
◇ 모범 사례와 관행 사이 큰 괴리있는 보안 업계
향후 2년 간 IoT 기기의 41%가 계정 및 권한 확인을 위해 디지털 인증서에 의존할 것으로 예상된다. 하지만 IoT 기기, 플랫폼, 데이터 저장소(repository)를 위한 암호화는 33% 증가에 그쳐 민감 데이터에 대한 잠재적 취약점이 될 수 있다.
IoT 보안 위협으로 응답자들은 악성코드 또는 기타 공격을 통한 IoT 기기 임의 조작(68%), 허가 받지 않은 사용자의 원격 조정(54%)을 꼽았으며, 패치 배포나 IoT 기기 업데이트 같은 악성코드 차단 방식으로는 통제 실효성이 없다고 답했다.
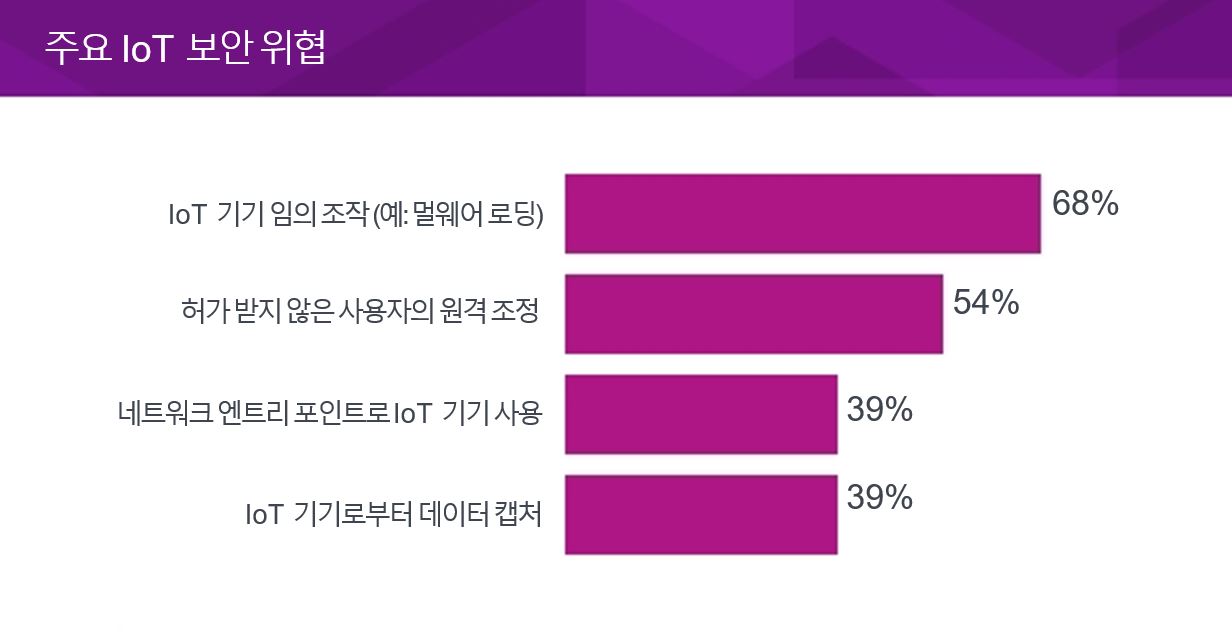
▲ 주요 IoT 보안 위협 [그래프=엔트러스트]
미국 국립표준기술연구소(NIST)는 인증기관(CA)용 암호화 모듈, 주요 복구 서버, OCSP(Online Certificate Status Protocol) 응답에 대해 FIPS 140-2 레벨 3 또는 그 이상의 인증을 권고한다. 응답자 39%가 하드웨어 보안 모듈(HSM)의 주된 사용처가 루트 발급 정책 인증기관을 위한 PKI 보안 유지라고 답했지만 HSM을 OSCP 설치에 사용하는 응답자는 12%에 불과했다. 이는 모범사례와 관행의 큰 괴리를 보여준다.
엔트러스트 디지털 솔루션 전략 부문 부사장인 존 그림(John Grimm)은 "기업은 IoT 같은 새로운 영역에서 보안 위협에 대응할 펌웨어 인증 등 보안 매커니즘 구축에 어려움을 겪고 있다"라며, "이번 연구 결과는 인증서 자동관리, 유연한 PKI 도입, HSM 등 모범사례에 기반한 강력한 보안의 필요성을 보여준다"라고 설명했다.