인더스트리 4.0 시대, 하드웨어 사이버 보안의 중요성
기사입력 2019.12.10 14:21
사이버 보안 달성하려면 새 산업 표준 충족해야
클라우드 통해서 타 공장 시스템과 상호작용 필요
네트워크 공격에는 심층 방어와 제로 트러스트
공장의 디지털화를 포함하는 인더스트리 4.0은 산업용 시장 영역의 기업 경영진들에게는 다른 많은 것들을 의미할 수 있다. 특히 디지털화로 인해 공장의 다양한 장치들이 스마트해지고 네트워크로 연결됨에 따라 사이버 보안이 더 중요해질 수가 있다.
예를 들면, 이는 공장 가동 비용을 절감하고 고객들에게 더 높은 가치를 제공하기 위해 더 높은 자동화 및 맞춤화 수준으로 공장을 탈바꿈하는 것을 뜻할 수가 있다.
시스템과 서브 시스템 공급사들이 공장의 장치들을 보다 스마트하게 제조함으로써, 더 방대한 멀티셀 시스템 및 엔터프라이즈 시스템 전반에 걸쳐서 제조 셀들의 실시간 의사결정과 자율적인 상호작용을 하게 할 수도 있다. 인더스트리 4.0 솔루션을 어떻게 활용할 것인가 하는 솔루션 채택 전략에 따라 이들 솔루션이 가치 사슬에 통합될 위치와 공장 내 통합의 깊이가 달라질 것이다.
공장 디지털화는 가치 사슬 전반에 변화를 가져오고 있으며, 기업의 매출과 지출 모두에 영향을 미친다. 이와 관련해 가장 많이 논의되는 것은 새로운 제품, 서비스, 또는 이 둘의 조합으로서 새로운 매출을 창출할 수 있게 해주는 혁신이다.
디지털 제조, 프로세싱 활용, 에지에서의 데이터 분석을 위해서는 새로운 제품 혁신이 요구되며, 메타데이터 수집은 제어, 유지관리, 활용을 최적화하는 새로운 서비스를 가능하게 한다. 다른 한편에서는 비용 절감을 위해 유통망 효율과 운영 성과를 향상하고자 하는 노력이 이루어지고 있다.
이러한 향상을 위해서는 공장에 보다 스마트한 제품과 서비스 도입이 필요하다. 인더스트리 4.0을 실현하려면 보다 혁신적인 제품을 사용해야 한다. 또한, 인더스트리 4.0 솔루션을 어떻게 활용할 것인가에 따라 사이버 보안 전략은 공장 내 디지털 솔루션의 성공적인 도입 및 확대를 보장하도록 달라질 것이다.
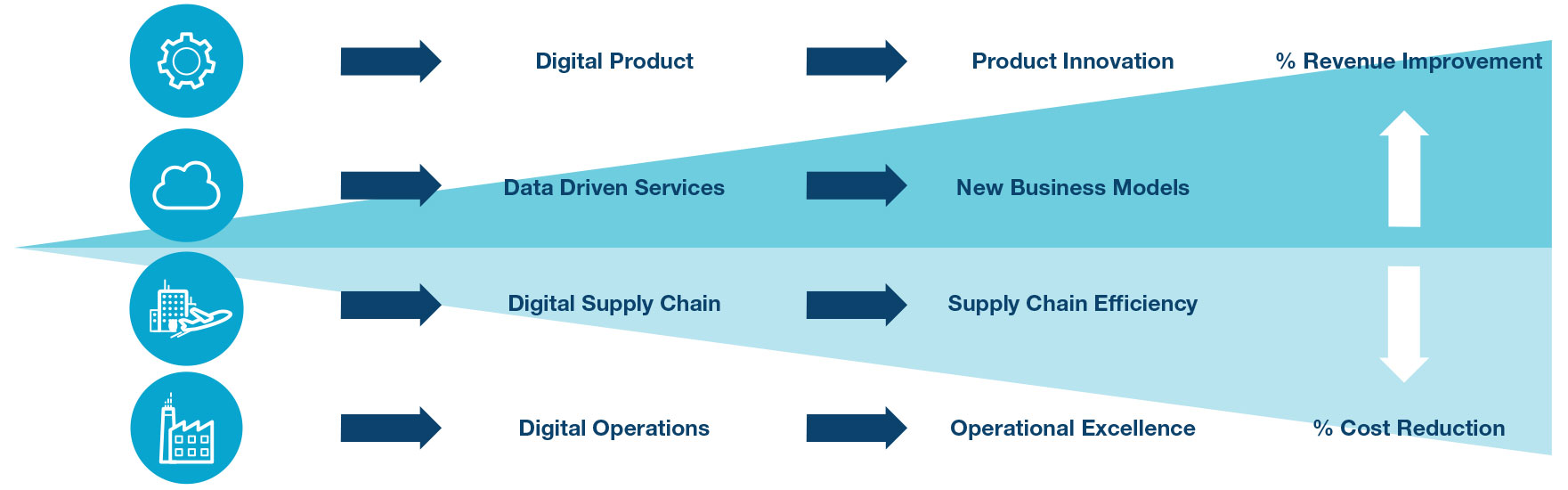
▲그림 1: 공장 디지털화는 가치 사슬 전반에 변화를 가져오고 있으며, 기업의 매출과 지출 모두에 직접 영향을 미친다
사이버 보안 전략은 또 디지털 솔루션이 산업용 제어 루프의 에지 상에 얼마나 널리 활용되고 있느냐에 따라 달라질 것이다. 기존의 산업 자동화 아키텍처는 사이버 보안 위협을 방어하기 위해서 필드 디바이스를 공장의 나머지 정보 시스템, 서비스, 애플리케이션으로부터 격리하는 방법을 썼다.
게다가 실제 필드 디바이스들은 통상적으로 데이터 교환이나 에지 프로세싱이 제한적인 포인트투포인트(Point-to-Point) 솔루션이므로, 사이버 보안 위험성이 어느 한 디바이스에서 전체 시스템으로 퍼지는 것을 방지한다. 이러한 아키텍처를 한꺼번에 바꾸기는 쉽지 않은 일이기 때문에 단계적인 접근법이 필요하다.
좀 더 공격적으로 인더스트리 4.0 솔루션을 도입하기 위해서는 공장에 첨단 기술을 어느 수준으로 통합할지, 그리고 인터스트리 4.0을 보다 적극적으로 활용하기 위해서는 사이버 보안을 어떻게 구현할지 결정해야 한다. 새로운 산업 자동화 아키텍처는 예전과는 전혀 다른 모습이 될 것이다.
기존에는 공장을 퍼듀 모델(Purdue model) 등에 따라 다섯 층위로 구분했지만, 미래의 공장 아키텍처는 이 모델을 따르지 않을 것이다. 미래의 필드 디바이스는 감지 및 작동하는 영역을 제조 실행과 제어와 결합할 것이다. 이들 디바이스는 공장의 통합 네트워크로뿐 아니라, 엔터프라이즈 시스템, 인터넷, 클라우드 서비스에도 직접 연결될 것이다.
따라서 어느 한 가지 디바이스만 보안이 뚫린다고 하더라도 전체 시스템의 사이버 보안이 크게 위험해진다. 미래의 인더스트리 4.0 아키텍처가 어떤 모습을 갖게 되든지, 최종적인 목표를 달성하기 위해서는 저마다 추구하는 디지털화 정도에 따라서 단계적인 접근법과 효과적인 사이버 보안 전략이 필요할 것이다.
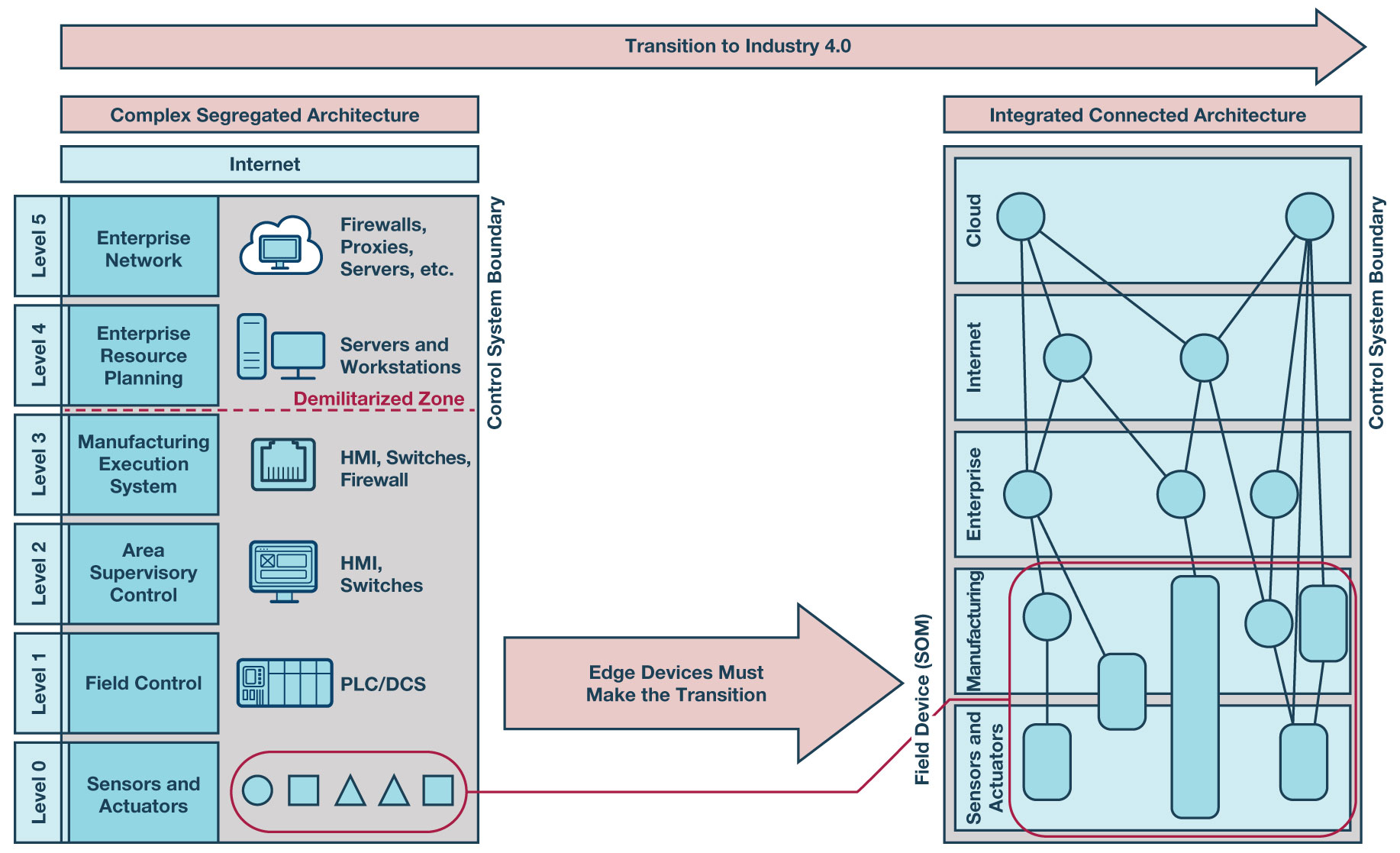
▲그림 2: 완벽한 디지털 인더스트리 4.0 공장으로의 이행
사이버 보안 인더스트리 4.0 실현을 위한 3단계
미래의 인더스트리 4.0이 어떤 모습일지에 대해서는 의견이 분분하다. 어떤 이들은 전통적인 공장 모습이 거의 그대로 남아 있을 것이라고 하고, 또 어떤 이들은 새로운 공장에서 예전 모습은 거의 찾아볼 수 없게 될 것이라고 한다. 하지만 모두가 인정하는 것은, 공장은 달라지고 있으며, 그러한 변화는 하룻밤 사이에 이루어지지 않는다는 것이다.
여기에는 명확한 이유가 몇 가지 있지만, 가장 기본적인 이유는 오늘날 현장에서 사용되고 있는 장비들의 수명이다. 이러한 장비들은 20년 혹은 그 이상으로까지 작동하도록 설계되었다. 이들 장비를 추가적인 기능이나 커넥티비티가 가능하도록 개조할 수 있지만, 그렇게 하는 데에도 하드웨어적인 설계 제약이 따르고 공장의 시스템 아키텍처 역시 어느 정도 부족한 부분을 감수해야만 한다.
사이버 보안 차원에서도 이러한 개조 장비는 늘 위험성을 내포한다. 보안성 면에서 안전한 디바이스가 되도록 하려면 보안적인 아키텍처와 시스템 설계가 필요하다. 보안 기능을 갖도록 디바이스를 개조하는 것은 어디까지나 임시방편일 뿐이며 사이버 보안 측면에서 취약점을 남길 수밖에 없다. 완전한 디지털화로 전환하려면 실시간 정보 공유 및 의사결정 능력을 떨어뜨리지 않으면서 사이버 공격을 막아낼 수 있는 높은 수준의 보안이 필요하다.
인더스트리 4.0의 사이버 보안을 위해서는 문제로부터 재빨리 회복하는 능력인 회복성(resiliency)은 사이버 보안을 실행하는 방법에 막강한 영향을 미칠 뿐 아니라 사이버 보안 인더스트리 4.0으로 나아가는 데 꼭 필요한 요소이기도 하다.
사이버 보안을 달성하기 위한 첫 번째 과제는 새로운 사이버 보안 산업 표준을 충족하는 것이다. 그러기 위해서는 이전과는 다른 접근법을 받아들이기 위한 변화가 필요하다. 기존에는 정보 기술(IT) 보안 솔루션을 사용해서 네트워크 트래픽을 격리시키고, 모니터링하고, 구성했는데, 인더스트리 4.0 공장에서는 이 방법으로는 신속하게 대응할 수 없다.
디바이스들이 연결되고 실시간으로 정보를 공유하기 때문에, 하드웨어 보안 솔루션은 공장의 디바이스들이 자율적으로 실시간 의사결정을 하면서 신속하게 대응할 수 있도록 해야 한다.
사이버 보안에 대한 접근법이 달라짐에 따라, 기업들 역시 새로운 과제들을 처리하는데 적응할 필요가 있다. 현재 많은 기업이 전통적인 엔지니어링 조직으로부터 분리되어 철저히 실무 프로젝트팀으로서 결합할 수 있는 형태로 사이버 보안 조직을 재편성하고 있다. 인더스트리 4.0을 달성하기 위해 가장 먼저 해야 할 일은 산업 표준 및 최선의 관례에 충실하게 사이버 보안 솔루션 전략을 실행할 수 있는 조직을 구축하는 것이다.
새로운 보안 표준을 충족할 수 있는 탄탄한 토대를 마련하고 제품 수명과 기업 전반에 걸쳐서 보안 요구 사항을 관리할 수 있는 장비를 갖췄다면 그다음에는 공장 셀 내에서 자율성을 높이는 문제로 눈을 돌릴 수 있다. 자율성은 공장 내의 디바이스들이 수신한 데이터에 기반해서 의사결정을 할 수 있을 만큼 충분히 스마트해야만 달성될 수 있다.
이러한 사이버 보안 접근법은 데이터가 생성된 곳에서 데이터의 신뢰성을 입증할 수 있는 에지 상의 디바이스를 구축하는 시스템 설계이다. 이렇게 하면 실제 외부 세계로부터 입력을 받아 이것이 신뢰할 수 있는 데이터인지 확인한 다음, 자율적으로 그에 따른 조처를 할 수 있는 사이버 보안 시스템을 통해 제공된 실시간 의사결정에 대해 확신을 가질 수 있다.
마지막 과제는, 공장을 클라우드로 연결할 뿐만 아니라 클라우드 서비스를 통해서 다른 공장 시스템과도 상호작용할 수 있도록 하는 것이다. 그러기 위해서는 디지털 솔루션의 전면적인 도입이 필요하며, 이렇게 했을 때라야만 완전한 디지털화 공장을 실현할 수 있을 것이다. 오늘날에도 디바이스들은 이미 클라우드에 연결되어 있으나 대부분의 경우 이는 데이터 수신용일 뿐이다. 이러한 데이터는 분석이 가능하며, 멀리 떨어진 공장에서 의사결정이 이루어질 수도 있다.
이러한 의사결정에 따라서 유지보수를 앞당기거나 늦출 수도 있고, 또는 자동화 공정을 조정할 수도 있다. 오늘날에는 이러한 의사결정을 클라우드에서 하는 것은 거의 드물고, 엔터프라이즈 시스템과 격리되어서 현장 자체 내에서 제어가 이루어진다. 공장에 고도의 자율성이 도입되면 클라우드 서비스를 통해서 모니터링과 제어를 하고 엔터프라이즈 시스템과 실시간 정보를 공유하는 것이 좀더 유기적으로 이루어질 것이다.
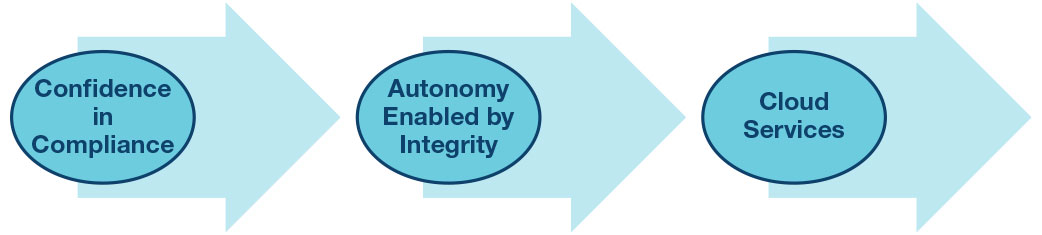
▲그림 3: 공장으로 자율성 도입
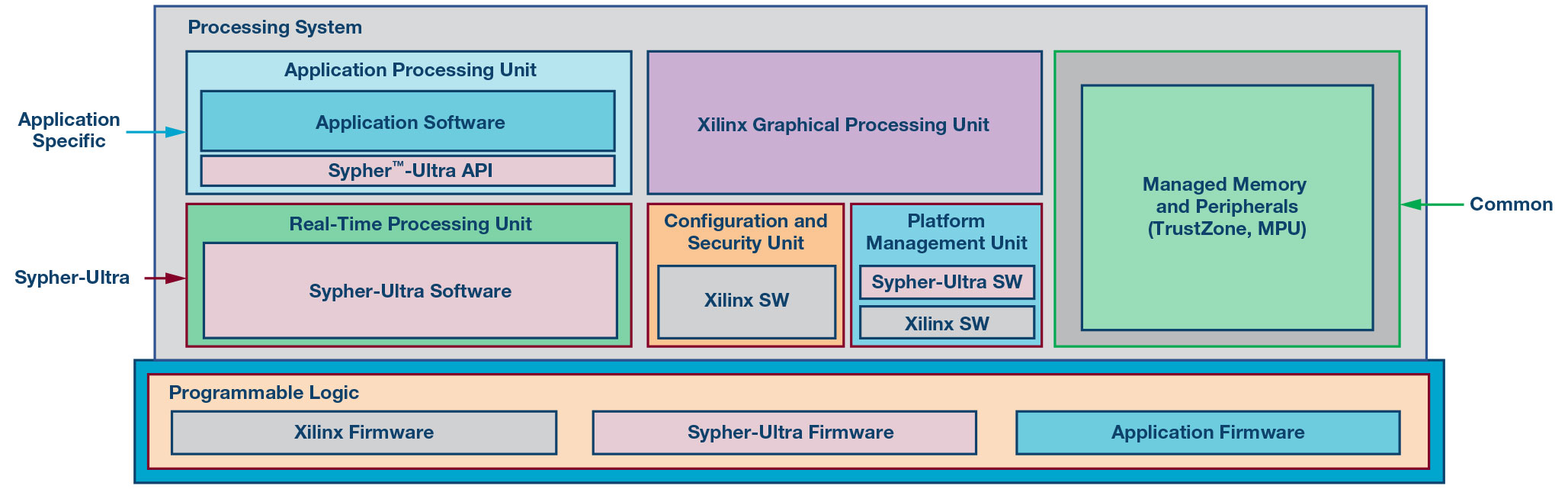
▲그림 4: ADI의 사이퍼울트라(Sypher-Ultra) 구현
하드웨어 보안을 사용한 커넥티드 공장
산업 표준이 요구하는 높은 수준의 보안성을 공장의 커넥티드 솔루션에 달성하려면 하드웨어 보안이 필요하다. 연결성이 높아진다는 것은 그만큼 위험성도 높아진다는 것을 뜻한다. 이러한 위협을 방어하려면 기존의 IT 보안 솔루션으로는 어렵고 디바이스 차원의 보안에 하드웨어 RoT(Root-of-Trust)를 결합해야 한다.
여러 디바이스들이 네트워크로 연결됐기 때문에 어느 한 디바이스가 뚫리면 이곳이 전체 시스템으로 들어가는 진입 지점이 될 수 있다. 그러면 이들 진입 지점 중 어느 한곳에서 유발된 피해가 전체 네트워크 피해로 확대되고, 주요 인프라를 취약하게 할 수 있다. 방화벽, 멀웨어 감지, 이상 감지를 기반으로 한 기존의 보안 기법은 지속적인 업데이트와 구성이 필요하며 사람의 실수가 개입되기 쉽다.
오늘날에는 네트워크를 통해 언제든 공격이 들어올 수 있다는 것을 고려해야 한다. 이러한 공격을 방어하기 위해서는 심층 방어(defense-in-depth)와 제로 트러스트(zero-trust) 기법을 도입해야 한다. 커넥티드 디바이스가 이상 없이 작동하고 있다는 것을 확신하기 위해서는 디바이스에 하드웨어 RoT가 필요하다. 오늘날의 디바이스에 올바른 하드웨어 보안 장치를 장착하는 것이 내일의 디지털 공장으로 전환하는데 필요한 핵심이 된다.
아나로그디바이스(ADI)는 자일링스의 ZUS+(Zinq UltraScale+ MPSoC) FPGA 제품을 사용해서 사이퍼울트라(Sypher-Ultra)를 개발했다. 사이퍼울트라는 다층 보안 제어를 사용하는 뛰어난 보장성의 암호화 시스템을 통해서 데이터 무결성에 대해서 높은 수준의 신뢰도를 제공한다. ZUS+의 보안성 토대에 ADI가 개발한 추가적인 보안 기능들을 사용해서 NIST FIPS 140-2, IEC 62443, 자동차 EVITA HSM 같은 보안 요구를 수월하게 충족할 수 있다.
사이퍼울트라는 임베디드 ZUS+와 최종 애플리케이션 사이에 위치하며 보안적인 작동을 위한 단일 칩 솔루션을 제공한다. 보장성이 높은 보안 능력을 제공하기 위해, 사이퍼울트라는 TEE(trusted execution environment)를 사용해서 보안적인 데이터를 위한 토대를 제공한다.
보안 관련 기능은 주로 실시간 프로세싱 유닛과 프로그래머블 로직에서 실행되고, 애플리케이션은 애플리케이션 프로세싱 유닛으로 손쉽게 추가할 수 있다. 개발 작업을 하기 위해서 복잡한 보안 설계와 인증을 전문가 수준으로 알 필요가 없으며, 매우 높은 수준의 보안 동작을 신뢰할 수 있다.
디지털 공장으로 전환하기 위해서 높은 수준의 디바이스 보안을 달성하는 것은 쉬운 일이 아니다. 보안을 구현하는 것은 전문성이 있어야 하는 복잡한 일이다. ADI의 보안 플랫폼은 산업 제어 루프의 에지 가까이에 보안을 구현할 수 있는 솔루션을 제공한다. 보안 설계, 보안 표준 인증, 취약성 분석 같은 복잡한 작업을 하지 않아도 되므로 개발 위험성을 낮추고 시간을 크게 절약할 수 있다.
솔루션은 일반적으로 사용되는 주요 플랫폼으로 사용하기 편리한 보안적인 API를 제공하므로 단일 FPGA로 고보장 보안과 고수준 애플리케이션이 공존할 수 있다.
ADI의 사이퍼울트라 제품은 자일링스 ZUS+ 제품을 사용해서 민감한 암호화 동작을 격리하고 민감한 IP에 대한 허가되지 않은 접근을 차단한다. 따라서 커넥티드 공장의 에지 상에서 하드웨어 보안을 위한 솔루션을 제공한다.
이 기사는 ADI의 사이버 보안 탁월성 센터의 에릭 할트헨(Erik Halthen) 산업용 솔루션의 보안 시스템 매니저의 '인더스트리 4.0에서 하드웨어 보안의 중요성(The Role of Hardware Security to Meet Industry 4.0 Aspirations)'란 제목의 글을 정리한 것입니다.
이수민 기자
관련 웨비나
많이 본 뉴스
[열린보도원칙] 당 매체는 독자와 취재원 등 뉴스이용자의 권리 보장을 위해 반론이나 정정보도, 추후보도를 요청할 수 있는 창구를 열어두고 있음을 알려드립니다.
고충처리인 장은성 070-4699-5321 , news@e4ds.com



.png)